You’re not here for beginner guidance, you already understand the fundamentals. This isn’t about defining carding; it’s about recognizing how sophisticated criminals target large retailers and the methods they use to avoid detection. Companies like Walmart face massive threats, and understanding these tactics is essential for anyone studying digital fraud.
Forget the rumors and misleading information circulating online. What follows is a realistic look at the strategies cybercriminals rely on, intended to help advanced readers strengthen their security awareness and understand how proper preparation and defensive measures play a major role in preventing fraud.
The Walmart Carding Method: What It Is, How It Works, and Most Importantly How You Can Protect Yourself in 2026
When you hear “The Walmart Carding Method,” don’t let flashy titles fool you. It’s not a legitimate “method” for success or profit. Instead, it points to a nefarious practice: using stolen credit/debit card data to shop in this case often targeting large retailers like Walmart to purchase gift cards or resalable goods, then turning them into cash or unauthorized benefits. In other words: fraud.
This article isn’t a guide for wrongdoing. Rather, it’s a wake-up call a deep dive into how carding works in 2026, why criminals still flock to mega‑retailers, and most importantly: how you can protect yourself.
Looking for a Reliable Legit CC Vendors for CC, Bank logins and Instant Transfer Vendor? Then Click the Link Below
Visit: Getbanklogs.com Contact Us: Click Here Shop link: Click Here
What Is “Carding”?
Definition and Origins
Carding refers to a form of payment fraud in which criminals use stolen credit or debit card information to make unauthorized purchases. Typically, carding starts with the theft or acquisition of card data — from physical theft to digital breaches and ends with misuse of that data to buy goods, gift cards, or cash‑equivalent items, often without the card owner ever knowing. Radware+2FraudNet+2.
The name “carding” likely stems from the idea of “testing cards” criminals check whether the card is active and valid before committing bigger fraud. Huntress+2Radware+2
Why Carding Gains Attention in Retail & E‑commerce
Thanks to e‑commerce boom, online shopping, and the rise of quick‑turn gift cards / resellable goods, carding has become a profitable and scalable criminal enterprise. Large retailers (both online and brick‑and‑mortar) offering a wide range of products — from electronics to gift cards — become attractive targets.
When you shop at a big store or website like Walmart, you’re part of a massive system that processes thousands of valid transactions — but that also offers cover for a few bad apples to slip in fraudulent ones.
How Carders Acquire Credit Card Data
Criminals don’t rely on one method; they employ a whole toolkit of dirty tricks. Here are some of the most common:
Phishing, Social Engineering, and Fake Websites
Often, carders impersonate trusted authorities — banks, well‑known companies, or even friends — using email, SMS, social media, or fake websites to trick users into revealing card info. Metro Credit Union+2Aura+2
They might say, “Your card’s been compromised — confirm here” — and if you click or comply, you hand them exactly what they need.
Skimming, Shimming, and Physical Card‑theft Methods
At physical checkout terminals, ATMs, gas pumps or self‑checkout stations, criminals may install a hidden device (a “skimmer” or “shim”) to copy card data from the magnetic strip or chip when you swipe your card. Wikipedia+2Metro Credit Union+2
Once the data is captured, thieves can either use it online or encode it onto a counterfeit physical card. Radware+2Department of Justice+2
Data Breaches, Malware, and Dark Web Marketplaces
Hackers may breach retail databases, payment processors, or e‑commerce sites and steal large batches of credit card details. These batches are sometimes sold on “carding forums” on the dark web. FraudNet+2Kasada+2
Malicious software—keyloggers, spyware or other forms of malware can also infect devices, silently capturing keystrokes or payment info whenever a user enters it. SEON+2Aura+2
Once criminals have card data, they might never use it themselves they could sell it to other criminals around the globe.
Swift Bank Transfers, Real Results: Don’t wait for financial stability! Receive $5k — $5M in your bank account within minutes at supremhackers.net. Don’t doubt, but ensure authenticity by asking for proof before proceeding!
Get Instant 50,000 to your bank account — Click Here Get Instant 100,000 to your bank account — Click Here
Step 1: Forum Integration
The Typical “Carding” Workflow
Understanding the flow helps you spot red flags — whether you’re a shopper or a retailer.
Step 1. Obtaining Stolen Card Data
As above: via phishing, malware, skimming, data breaches, or dark‑web purchases.
Step 2. Card Testing / Validation
Criminals or automated bots make small transactions often minimal purchases to check whether the card works, whether it has balance, whether the issuing bank flags it. This method limits risk and avoids immediate detection. Huntress+2Radware+2
If the small purchase goes through, criminals mark the card as “live,” and flag it for bigger misuse.
Step 3. Large Purchases or Gift Cards, Resale or Cash-Out
Once a card is validated, it’s used for high-value purchases electronics, gift cards, goods easily resold. Gift cards are popular because they can be quickly converted into cash or sold online with anonymity. Metro Credit Union+2Aura+2
Step 4. Using “Drop Addresses” to Avoid Detection
To avoid traceability, criminals often ship purchased items to “drop addresses”: vacant houses, apartments, or third-party locations — not their real home. Department of Justice+1
This way, by the time a victim or bank catches on, the items are out of easy reach, and the fraudsters remain anonymous.
Why Retailers Like Walmart Are Frequent Targets
Size, Volume, and Variety of Products
Retail giants like Walmart process thousands of transactions daily. The sheer volume provides hiding spaces for a few fraudulent orders — easier for bad actors to “blend in.”
Gift Cards & Resellable Items as Easy Cash‑Out Goods
Gift cards, electronics, high‑demand items turn fraud into fast cash. Once purchased with stolen cards, these goods are resold — hard to trace.
Self‑Checkout, Online Checkout, and Other Vulnerable Entry Points
Self‑checkout kiosks, online ordering, and minimal identity verification open more windows for carders. Skimming/shimming at self-checkout and card-not-present (online) fraud are both common. Aura+2SEON+2
The Consequences Who Loses What
Victims Unauthorized Charges, Identity Theft Stress
If your card data gets stolen, you may wake up to unexpected charges, drained balances, or fraudulent gift card purchases. The stress, time for reporting, and the hassle of replacing cards can be significant.
Retailers Chargebacks, Losses, Fraud Risk, Trust Issues
Every fraudulent order often ends in a chargeback. Businesses lose money on goods shipped, processing fees, and risk damaging relationships with payment processors.
Wider Economy Incentive for More Sophisticated Attacks
The more lucrative carding becomes, the more criminals invest in automation, malware, and advanced techniques — pressure mounts on retailers, banks, and consumers to stay one step ahead.
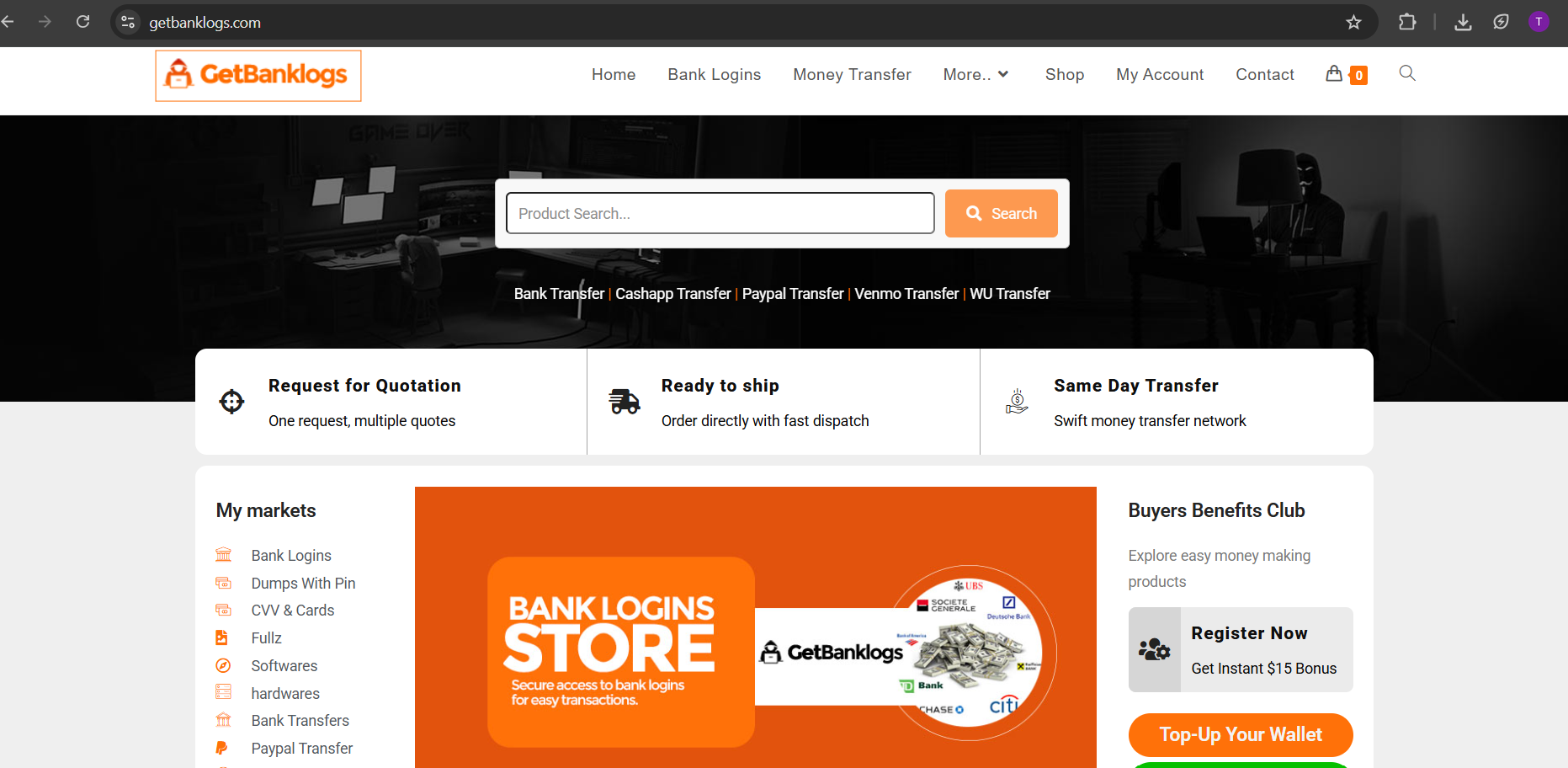
1. Sudohackers.com (Legit CC Vendors)
Sudohackers.com Known for high-balance worldwide dumps, money transfers, bank logs, and gift cards. Their CC sites and bins are often fresh. Strong reputation on several Russian-language forums. Visit https://getbanklogs.com/
Legal and Ethical Implications
What the Law Says — Fraud, Theft, Money Laundering
Carding is not “hacking for fun.” It’s theft, fraud, often money‑laundering when goods are converted into cash or resold. Per courts and law enforcement, using or selling stolen card data, ordering items with it, or shipping to drop addresses are illegal activities subject to serious criminal penalties. Department of Justice+1
Risks of Drop‑Shipping Fraudulently Obtained Goods
Even third parties or unwitting drop‑address holders may face legal risks if found complicit. The resale market for stolen‑item goods is often surveilled by law enforcement.
Ethically, carding erodes trust in online retail, damages consumer confidence, and hurts legitimate buyers and sellers.
How Carding Fraud Has Evolved by 2025–2026
Automation & Bot Networks
Carders now rely heavily on bots that can attempt thousands of transactions per minute, automating the “validate card, buy gift card, move on” loop — making detection and blocking much harder. Radware+2HUMAN Security+2
Shift to Online‑Only Fraud (“Card‑Not‑Present” Transactions)
With more buyers shopping online and retailers offering robust e‑commerce platforms, criminals increasingly favor “card‑not‑present” purchases — where only card numbers, CVV, and billing addresses are needed, no physical card required. Wikipedia+2Aura+2
Use of Proxy / VPN / Geolocation Spoofing
To escape detection, criminals often hide behind proxies, VPNs or spoofed geolocations — making their actions appear as if coming from legitimate users in different countries or regions. Anura+1
They may also use temporary emails, fake shipping addresses and other evasive tactics to avoid triggering fraud warnings.
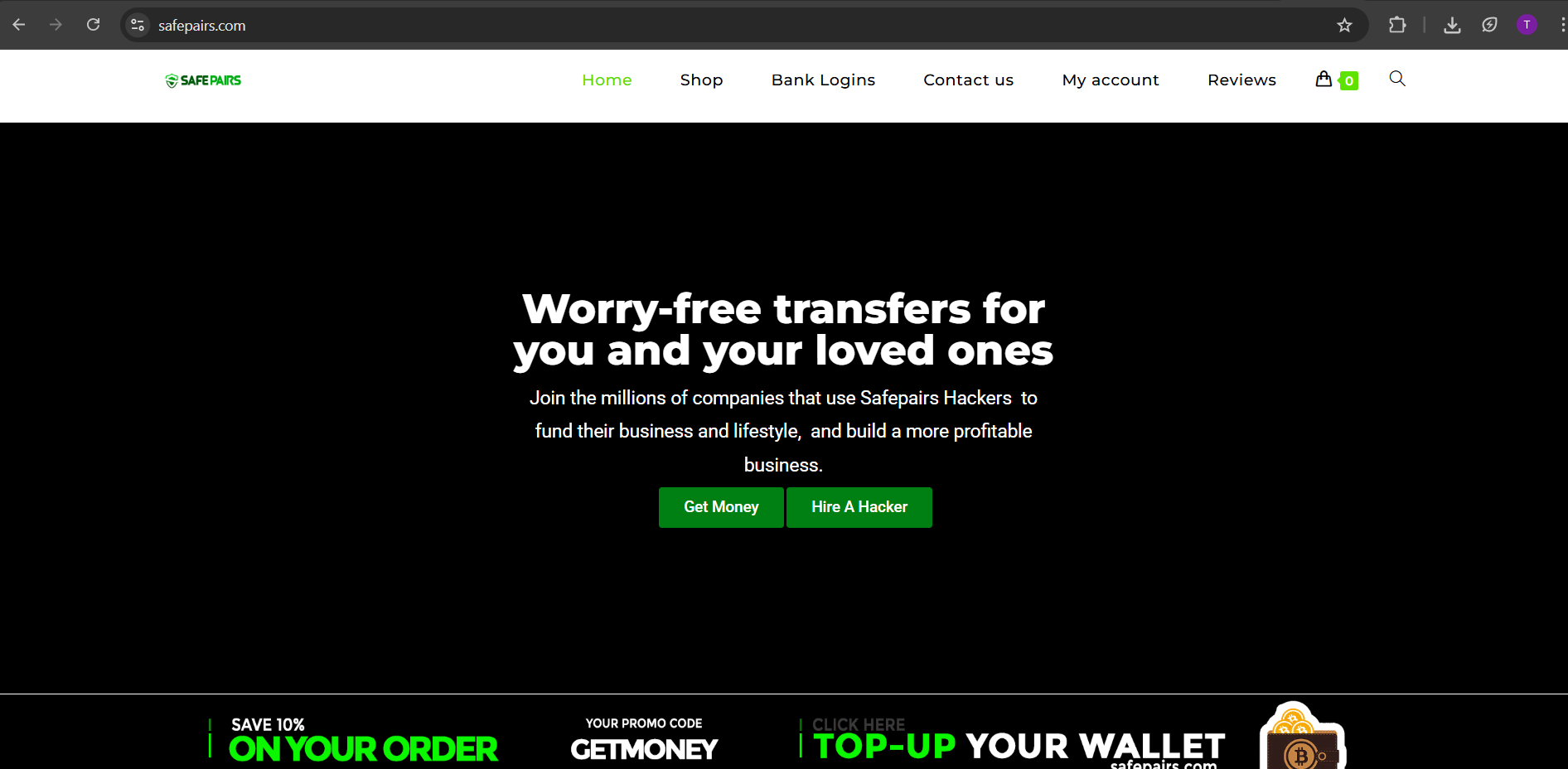
safepairs.com
A longstanding name. They’ve rebranded a few times, which is a good sign of operational security. They offer a wide range, from standard money transfers, PayPal transfer, bank logs, Zelle Transfer, Venmo Transfer and Western Union Transfers to specialized requests. Visit: http://safepairs.com
How Retailers are Fighting Back Security Measures
Retailers and payment processors are not sitting idle. They deploy multiple layers of protection against carding fraud:
EMV Chip Terminals, Contactless Payments
Using EMV chip cards or contactless (tap-to-pay) reduces risk compared to magstripe swiping. Chips generate unique codes per transaction — harder to clone or reuse. Wikipedia+2Arkose Labs+2
Anti‑Fraud Software: Velocity Checks, CAPTCHA, Device Fingerprinting
E‑commerce platforms now implement velocity checks (limiting the number of transactions per card in a period), CAPTCHAs, and device fingerprinting to block bots and suspicious activity. Radware+2Stripe+2
Geolocation & IP Monitoring, Billing vs Shipping Address Checks
Payment processors compare billing address, shipping address, IP location — mismatches or impossible combinations can trigger automated rejections or human review. Anura+2Arkose Labs+2
Multi‑Factor Authentication, 3D Secure & Verification Protocols
Systems like 3D Secure (for example “Verified by Visa” / “Mastercard SecureCode”) require an extra step — OTP, SMS, or biometric check — making card‑not‑present fraud harder. Aura+2Arkose Labs+2
Merchants may also flag high-risk transactions (e.g. unusually frequent orders, same card across many accounts) for manual review.
What You As a Shopper Can Do to Protect Yourself
You don’t have to wait for banks or retailers alone to protect you. There are smart, practical steps you can take daily:
Use Credit Cards, Not Debit Cards (When Possible)
Credit cards generally offer stronger fraud protection than debit cards. If fraud occurs, you’re less likely to lose personal funds — and disputes are easier to handle.
Prefer Contactless / Tap-to-Pay / EMV Chip Over Swiping
Whenever possible, choose chip or tap payments instead of swiping. It’s safer and less vulnerable to skimming or cloning.
Monitor Account Activity, Enable Alerts, Check Statements Frequently
Turn on purchase alerts, review bank statements regularly, and report suspicious charges immediately. Early detection reduces damage.
Avoid Unfamiliar Sites, Links, Emails — Don’t Share Financial Info Online
Phishing remains a major entry point. Don’t click suspicious email links or provide card details on untrusted websites — especially after receiving unsolicited messages.
Consider Identity Theft Protection & Use Strong Passwords / 2FA
Use strong, unique passwords for online accounts, enable two‑factor authentication, and consider using identity‑theft protection services or banking alerts.
Let’s be clear: free dumps with pin do not exist. Any site offering this is 100% a scam, a honeypot, or malware distribution. It’s the oldest trick in the book. Quality data has value. Anyone giving it away is lying. The only “free” thing you’ll get is your wallet drained or your door kicked in.
What to Do If You Suspect Fraud / Carding
Immediately Contact Your Card Issuer / Bank
If you notice unauthorized charges or suspicious activity contact your card issuer at once. They can freeze or cancel the card and issue a new one.
Freeze the Card, Change Passwords, Review Other Accounts
Don’t just stop at one card update passwords on related accounts (email, online retailers), monitor other payment methods, check for suspicious login attempts.
Report to Authorities, Law Enforcement & Retailer Fraud Departments
Report the incident to your bank, retailer (e.g. Walmart Fraud Department), and local authorities if necessary. This helps track patterns and prevent further misuse.
Why Awareness & Education Matter More Than Ever in 2026
As fraudsters grow more sophisticated — with AI‑powered bots, globalized fraud rings, and advanced evasion techniques — staying informed is your first line of defense.
Consumers who understand how carding works are less likely to fall victim. Retailers who learn these patterns can tighten security. And collectively, we make the shopping ecosystem safer.
Remember: fraud thrives in ignorance and fear. A little awareness can go a long way.
Final Thoughts Stay Safe, Stay Smart
Carding isn’t some distant hacker-movie plot. It’s real, ongoing, and often hits unsuspecting shoppers and retailers sometimes big ones like Walmart. But you don’t have to be a victim. With vigilance, smart payment choices, and secure habits, you can shut down many common fraud attempts before they even begin.
Your credit card information is like a key treat it like gold. Guard it, monitor it, and use common sense.
FAQs
Q1: What is the difference between carding and credit card cloning?
Carding is a broader term describing fraud using stolen card data often online. Cloning (or skimming/shimming) refers to copying the physical card data (mag‑stripe or chip) to create a counterfeit card for in‑person use. Carding might involve cloning, but not always.
Q2: If I use a chip card or tap-to-pay, am I completely safe?
No — while chip and contactless payments are safer than magnetic‑stripe swiping, they don’t protect against all fraud types, especially online (card‑not‑present) fraud or phishing that steals card numbers.
Q3: I got a weird small charge on my card does that mean I’m being “carded”?
Possibly. Carders often run small test transactions to validate cards. If you see unfamiliar small charges, it’s smart to monitor closely, contact your bank, and consider canceling the card if needed.
Q4: What is a “drop address” and why is it used in carding?
A drop address is a location (vacant house, third‑party address, empty storage unit) where fraudulently purchased items are sent so the criminals avoid traceability. It helps them hide identity and evade law enforcement.
Q5: How can merchants detect and stop carding on their website?
Merchants can implement anti-fraud tools: velocity checks (limit rapid transactions), CAPTCHA / bot detection, device fingerprinting, billing‑vs‑shipping address verification, geolocation monitoring, and require stronger authentication (e.g. 3D Secure).









Leave a comment